Social Engineering for Security Attacks: تفاوت میان نسخهها
(←چکیده) |
|||
| خط ۳: | خط ۳: | ||
== چکیده == | == چکیده == | ||
Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional "con" in that it is often one of many steps in a more complex fraud scheme. | |||
The term "social engineering" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals. | |||
== مقدمه == | == مقدمه == | ||
نسخهٔ ۱۲ نوامبر ۲۰۱۶، ساعت ۰۳:۰۷
Social Engineering for Security Attacks
چکیده
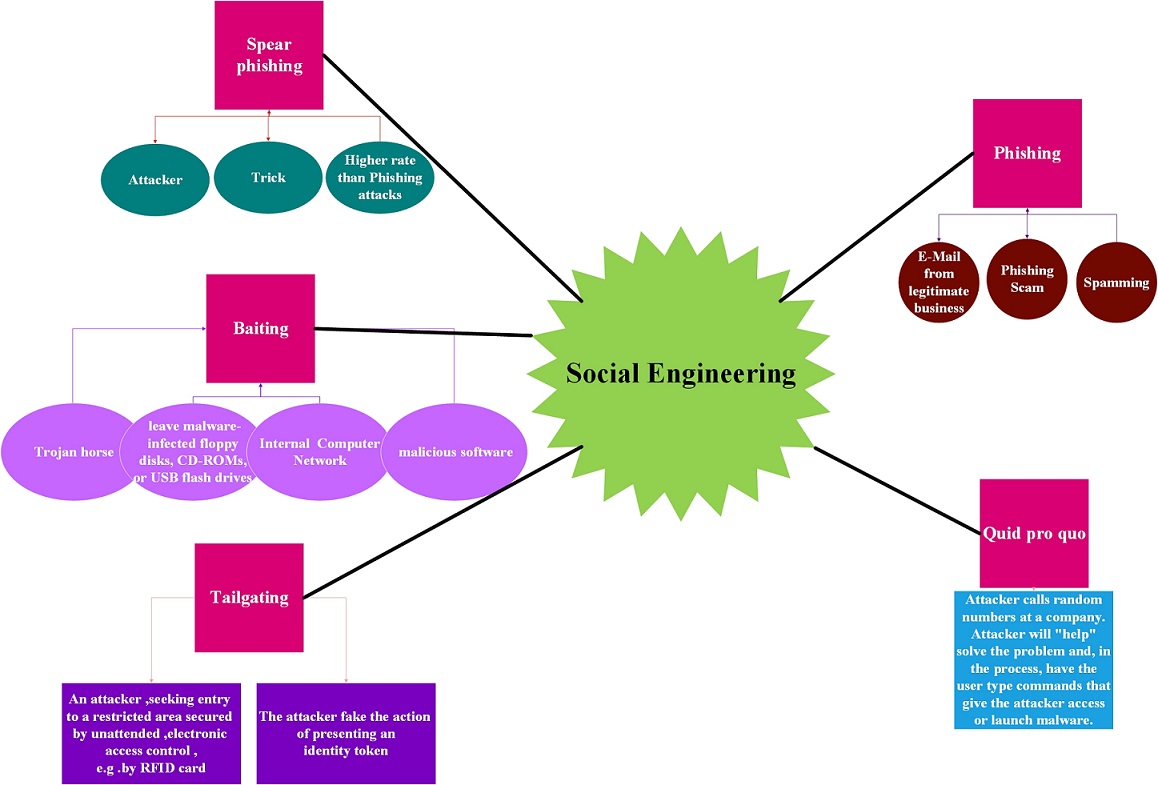
Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional "con" in that it is often one of many steps in a more complex fraud scheme.
The term "social engineering" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.
مقدمه
Social Engineering is a kind of advance persistent threat (APT) that gains private and sensitive information through social networks or
other types of communication. The attackers can use social engineering to obtain access into social network accounts and stays there
undetected for a long period of time. The purpose of the attack is to steal sensitive data and spread false information rather than to
cause direct damage. Such targets can include Facebook accounts of government agencies, corporations, schools or high-profile users. We
propose to use IDS, Intrusion Detection System, to battle such attacks. What the social engineering does is try to gain easy access, so
that the attacks can be repeated and ongoing. The focus of this study is to find out how this type of attacks are carried out so that they
can properly detected by IDS in future research.
بررسی ادبیات موضوع
بدنه تحقیق

نتیجه گیری
مراجع =
1 How difficult is it to carry out an APT attack? (n.d.). Retrieved May 07, 2014, from http://www.cbronline.com/news/cybersecurity/data/how-difficult-it-is-to-carry-out-an-atp-attack-4261415.
2 Spear-phishing statistics from 2014-2015 - InfoSec Resources. (2015, August 19). Retrieved June 08, 2016, from http://resources.infosecinstitute.com/spear-phishing-statistics-from-2014-2015.
3 Micro, T. (2012). Spear-Phishing Email: Most Favored APT Attack Bait. Trend Micro, http://www.trendmicro.com.au/cloud-content/us/pdfs/security-intelligence/white-papers/wp-spear-phishing-email-most-favored-apt-attack-bait.pdf (accessed 1 October 2014).
4 "Hack Like a Pro: How to Spear Phish with the Social Engineering Toolkit (SET) in BackTrack." Web log post. WonderHowTo. N.p., 2104. Web. 8 June 2016. <http://null-byte.wonderhowto.com/how-to/hack-like-pro-spear-phish-with-social-engineering-toolkit-set-backtrack-0148571/>.
5 D. Shallcross , R. Izmailov , L. Ness , A. McIntosh , D. Bassu, Centralized multi-scale singular value decomposition for feature construction in LIDAR image classification problems, Proceedings of the 2012 IEEE Applied Imagery Pattern Recognition Workshop (AIPR 2012), p.1-6, October 09-11, 2012 [doi>10.1109/AIPR.2012.6528195]
6 Y. Rossikova, J, J. Li and P. Morreale, "Intelligent Data Mining for Translator Correctness Prediction", CloudSecurity2016, Columbia unviersity NYC, April 2016.